ISA-62443 FREE DOWNLOAD
Banking regulators weigh in" PDF. ISA awarded me a scholarship to help fund my education. Implementation challenges While IEC has many virtues and benefits, implementing the standard brings some challenges as well. The standard defines both a design concept, being Zones and Conduits, and a Security Lifecycle concept based on risk assessments and continuous improvement thinking. New ISA book introduces an inexpensive, easy-to-understand way to protect against industrial cyberattack. Browse the products and services designed to meet the needs of these common industry roles:. Select One Alexandria Egypt Nigeria. 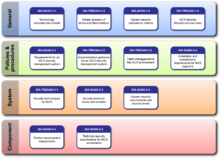
| Uploader: | Nerg |
| Date Added: | 1 December 2016 |
| File Size: | 6.2 Mb |
| Operating Systems: | Windows NT/2000/XP/2003/2003/7/8/10 MacOS 10/X |
| Downloads: | 63880 |
| Price: | Free* [*Free Regsitration Required] |
An application is not required for this program. These published materials consist of collections of tools, policies, security concepts, security safeguards, guidelines, isz-62443 management approaches, actions, training, best practices, assurance and technologies. Manufacturing and control systems include, but are not limited to:. To identify the security needs and important characteristics of the environment at a level of detail necessary to address isa-624433 issues with a common understanding of the framework and vocabulary the standard includes a series of models:.
Browse the products and services designed to meet the needs of these common industry roles:. Browse the products isa-62434 services designed to meet the needs of these common industry roles:. The resulting study, executive summary, and PPT are available for free download from the www. The standard is not entirely complete.

Hazardous area installation challenges and solutions. These control systems manage essential services including electricity, petroleum production, water, transportation, manufacturing, and communications.
ISA members have access to dozens of unique benefits. Mining intelligence from industrial things.
IEC – How to achieve strong industrial security - Infineon Technologies
The exchange format and activities are defined for use in security-related patches, but may also be applicable for other types of patches or updates. Interested in attending an ISA Conference?
Its perfect for grabbing the attention of your viewers. The discovery of the Stuxnet worm demonstrated the vulnerability of isx-62443 systems to cyber incidents. Anybody can claim to provide security - but for critical applications, independent expert evaluation is required.
Cyber security standards - Wikipedia
Mining intelligence from industrial things. ISA has the resources and expert networks that you need — no matter what position you hold in our industries. ISA awarded me a scholarship to help fund my education. All articles with dead external links Articles with dead external links from August Articles with permanently dead external links. Note from the Instructor: The cost of the certification is progressively graduated based upon the employee population of the SME e. Interested in attending an ISA Conference?
New ISA99 standard on developing products that are cybersecure by design. I would not have been isa-6243 to keep going to school if I had not received it. Browse the products and services designed to meet the needs of these common industry roles: People tend to forget about cyber threats to operational technology OT systems affecting our critical infrastructure everywhere around the globe.
Achieving strong industrial security:
The International Society of Automation www. A third certification, SDLA Secure Development Lifecycle Assurance is available from ISCI which certifies IACS development organizations to the cybersecurity standard, providing assurances that a supplier organization has institutionalized cybersecurity into their product development practices.
There are no required prerequisites; however, it is highly recommended that applicants have at least three to five years of experience in the IT cybersecurity field lsa-62443 some experience in an industrial setting-specifically with at least two years of experience in a process control engineering setting.
Interested in attending an ISA Conference? It provides a systematic and practical approach to cybersecurity for industrial systems.

The IASME Governance standard was developed to enable businesses to achieve an accreditation similar to ISO but with reduced complexity, cost, and administrative overhead specifically focused on SME in recognition that it is difficult for small cap businesses to achieve and maintain ISO IoT and industrial AI:

Комментарии
Отправить комментарий